In higher education, complex and widely distributed digital networks present unique security challenges. They manage student records, financial systems, research databases, intellectual property, and cloud-based learning platforms, all while supporting open collaboration and academic freedom. This combination of sensitive data and open access creates significant cybersecurity exposure. Educational institutions are not only centers of knowledge but also repositories of valuable information, making them attractive targets for cybercriminals.
The financial and operational consequences of cyber incidents in education are substantial. According to IBM’s Cost of a Data Breach Report 2025, the global average cost of a data breach reached $4.45 million. For institutions operating under limited budgets, such losses can disrupt teaching, research, and administrative functions. Strengthening cybersecurity in higher education institutions requires clear strategies that address governance, technology, people, and risk management in an integrated way.
The Evolving Cyber Threat Landscape in Higher Education
Higher education environments differ from corporate enterprises due to their decentralized governance, diverse user groups, and collaborative research partnerships. Open Wi-Fi networks, personal devices, remote learning platforms, and third-party research collaborations expand the institutional attack surface.
Educators currently face ransomware attacks that adapt rapidly to evolving campus defenses. Numerous studies highlight that ransomware continues to impact the education sector at significant rates. Phishing campaigns, credential theft, and exploitation of unpatched systems are common entry points.
Research-intensive institutions face additional risks due to the value of their intellectual property. Sensitive research data, especially in science and technology fields, can be targeted for espionage or financial gain. These realities underscore the need for structured, proactive cybersecurity strategies.
Major Cybersecurity Strategies for Higher Education Institutions
To effectively address evolving digital threats, higher education institutions must implement structured, institution-wide cybersecurity strategies that safeguard data, research, and academic operations.
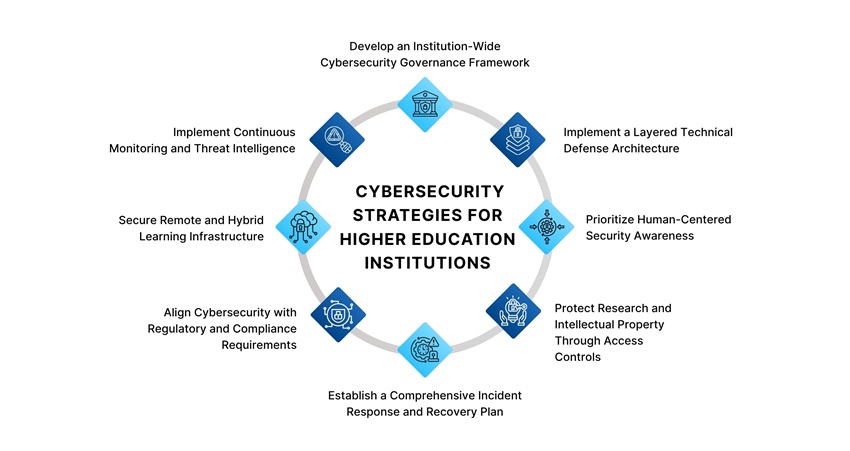
1. Develop an Institution-Wide Cybersecurity Governance Framework
A foundational strategy involves embedding cybersecurity into institutional governance. Security should not function solely as an IT responsibility but as an enterprise-level priority. Establishing a formal cybersecurity governance framework ensures accountability and strategic alignment.
Leadership teams should define clear roles, risk tolerance levels, reporting structures, and incident escalation procedures. Regular risk assessments help identify vulnerabilities across academic departments, administrative systems, and research centers. Integrating cybersecurity into strategic planning ensures sustained commitment rather than reactive action.
A documented cybersecurity roadmap aligned with institutional goals enables coordinated investment, compliance tracking, and performance evaluation.
2. Implement a Layered Technical Defense Architecture
A multi-layered defense model significantly reduces institutional exposure. Instead of relying on a single security mechanism, institutions should adopt a defense-in-depth approach.
Key measures include:
- Multi-factor authentication for all privileged and remote accounts
- Network segmentation separating research data from general campus traffic
- Endpoint detection and response systems to monitor device activity
- Regular patch management and vulnerability scanning
- Encryption for sensitive data both in storage and transmission
Cloud environments require particular attention. As institutions expand digital learning and administrative services into cloud platforms, configuration monitoring and shared-responsibility awareness become essential. Secure, offline backups should be maintained and tested regularly to mitigate ransomware risks.
3. Prioritize Human-Centered Security Awareness
Technology alone cannot eliminate cybersecurity risks. Human error remains a leading cause of breaches. Social engineering attacks, including phishing and credential harvesting, exploit behavioral vulnerabilities.
The 2025 Verizon Data Breach Investigations Report emphasizes the significant role of human factors in security incidents. Continuous awareness initiatives are therefore critical.
Institutions should implement structured training programs for students, faculty, researchers, and administrative staff. Training should address password hygiene, data handling practices, and secure remote access. Simulated phishing campaigns can help assess awareness levels and improve preparedness.
Clear reporting channels must be established so that suspicious activities can be flagged quickly. Encouraging a culture of transparency strengthens early detection and response.
4. Protect Research and Intellectual Property Through Access Controls
Research data requires specialized protection strategies. Implementing the principle of least privilege ensures that individuals access only the information necessary for their responsibilities. Role-based access controls limit exposure and reduce insider risk.
Data classification policies help institutions identify high-risk assets and allocate resources appropriately. Sensitive research environments should operate within segmented networks with restricted external access.
Third-party collaborations introduce additional vulnerabilities. Vendor risk assessments and secure data-sharing agreements are essential to maintain control over institutional data. Monitoring external access helps prevent unauthorized data exfiltration.
5. Establish a Comprehensive Incident Response and Recovery Plan
Even the strongest preventive measures cannot guarantee immunity from cyber incidents. A formal incident response plan ensures swift, coordinated action when breaches occur.
Response plans should define roles, communication protocols, legal obligations, and technical containment procedures. Conducting regular tabletop exercises helps leadership and IT teams rehearse real-world scenarios, improving readiness.
Post-incident evaluations identify root causes and guide corrective measures. Secure backups, regularly tested for reliability, enable operational recovery without paying ransom demands.
6. Align Cybersecurity with Regulatory and Compliance Requirements
Higher education institutions function within intricate regulatory frameworks that oversee data privacy, research ethics, and financial adherence. Compliance alignment reduces legal exposure and strengthens institutional credibility.
Periodic audits, documentation of security controls, and automated monitoring tools can streamline compliance management. Integrating regulatory obligations into broader cybersecurity strategy prevents fragmented efforts and enhances efficiency.
7. Secure Remote and Hybrid Learning Infrastructure
The expansion of online and hybrid learning has permanently increased digital dependency. Learning management systems, virtual classrooms, and remote collaboration tools must be secured through strong authentication and secure configuration settings.
Institutions should regularly assess third-party digital learning platforms for security compliance. Guidance for students and staff on securing personal devices and home networks reduces vulnerabilities associated with remote access.
Secure digital infrastructure ensures continuity of education even during disruptions.
8. Implement Continuous Monitoring and Threat Intelligence
Cyber threats evolve rapidly, making static security controls insufficient. Continuous monitoring systems collect and analyze network logs to detect anomalies in real time.
Security information and event management systems enhance visibility across distributed networks. Regular penetration testing and vulnerability assessments identify weaknesses before attackers exploit them.
Staying informed about global threat trends allows institutions to adjust defenses proactively. Cybersecurity should function as a continuous adaptation to emerging threats rather than a one-time initiative.
Building a Cyber-Resilient Academic Culture
Cybersecurity resilience in higher education is not achieved solely through tools and policies; it is shaped by institutional culture. Universities are inherently open environments that promote collaboration, experimentation, and digital exploration. Balancing openness with security requires shared responsibility across the campus community.
Embedding cybersecurity awareness into academic orientation programs, research onboarding processes, and leadership training helps normalize security-conscious behavior. When faculty, students, researchers, and administrators recognize their role in safeguarding institutional systems, cybersecurity becomes part of everyday practice rather than an isolated IT directive.
A cyber-resilient academic culture encourages proactive reporting, responsible data handling, and informed digital decision-making. Over time, this cultural integration strengthens the institution’s overall security posture and reduces vulnerability to evolving threats.
Benefits of Strong Cyber Defenses in Educational Institutions
Robust cyber defenses strengthen institutional resilience, helping educational environments remain secure, reliable, and future-ready amid evolving technological and security challenges.
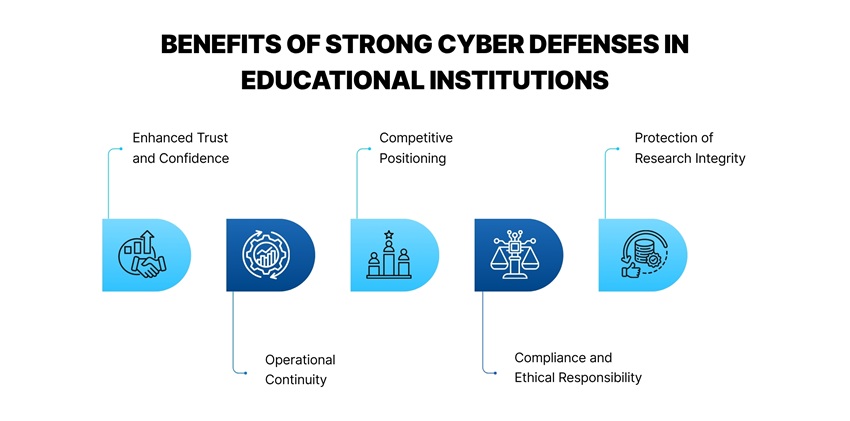
- Enhanced Trust and Confidence: Strong cybersecurity reassures students, faculty, staff, funders, and partners that their data and academic contributions are protected. This trust supports recruitment, enrollment, and sustained collaboration.
- Operational Continuity: With effective security measures in place, institutions can minimize downtime and ensure academic and administrative systems remain available even in the face of attempted attacks. Preparedness reduces the ripple effects of disruption on teaching, research, and student services.
- Competitive Positioning: As cyber threats become more sophisticated, institutions with advanced defenses gain strategic advantage. Prospective students and research partners increasingly view cybersecurity as a measure of institutional reliability. Organizations that publicly demonstrate strong security protocols can differentiate themselves in a crowded higher education landscape.
- Compliance and Ethical Responsibility: Adopting comprehensive cybersecurity measures helps institutions comply with data privacy laws and research ethics standards. Compliance reduces legal risk and reinforces ethical stewardship of sensitive information, strengthening institutional integrity.
- Protection of Research Integrity: Secure environments enable researchers to collaborate confidently, exchange findings, and build knowledge without fear of unauthorized access or data theft. Given the increasing value of academic research in global innovation, safeguarding intellectual assets supports both institutional prestige and societal advancement.
Risks of Inaction and Inadequate Cybersecurity
Failing to prioritize cybersecurity can leave higher education institutions vulnerable to serious disruptions and long-term institutional challenges.
- Operational Disruption
Cyber incidents, such as ransomware attacks and distributed denial-of-service (DDoS) events, can halt online learning platforms, administrative systems, and research workflows. As described in research exploring cybersecurity frameworks for higher education, these institutions are particularly vulnerable due to their open networks and decentralized systems.
- Financial Burden
Data breaches and recovery efforts impose significant financial costs. In addition to remediation expenses, institutions may incur fines related to data protection compliance, loss of research funding due to interrupted grants, and increased insurance premiums. These unforeseen costs can strain limited education budgets and divert resources away from academic priorities.
- Reputational Damage
Trust is central to a university or college’s mission. Students trust institutions with personal data, and research partners rely on them to protect sensitive findings. Public disclosure of security failures can discourage prospective students and collaborators, eroding long-term reputation and competitiveness.
- Intellectual Property Loss
Research universities often hold valuable proprietary information. Without adequate protection, breakthroughs in science, technology, and health fields can be stolen or misused, undermining both academic and societal progress.
Also Read - Cybersecurity In Education: Building Resilient Institutions
Conclusion
Higher education institutions face a unique cybersecurity challenge: safeguarding valuable academic, research, and personal data while preserving open, collaborative environments. The financial, reputational, and research consequences of cyber incidents can significantly disrupt institutional missions. Strengthening cybersecurity therefore demands an integrated approach that combines strong governance, layered technical defenses, continuous monitoring, compliance alignment, structured incident response planning, research data protection, and ongoing security awareness initiatives. More than a technical necessity, cybersecurity now sits at the core of institutional risk management and digital governance; embedding it into institutional leadership and culture ensures resilience, protects innovation, and enables institutions to continue advancing knowledge and societal progress.
Frequently Asked Questions
1. Why are higher education institutions frequent targets for cyberattacks?
Higher education institutions manage large volumes of sensitive data, including student records, financial information, and valuable research. Their open academic networks, collaborative environments, and extensive use of personal devices create multiple entry points for cybercriminals, making them attractive targets.
2. What are the most common cybersecurity threats faced by universities and colleges?
Common threats include ransomware attacks, phishing campaigns, credential theft, data breaches, and exploitation of unpatched systems. These threats often target research databases, student information systems, and online learning platforms.
3. How can higher education institutions strengthen their cybersecurity defenses?
Institutions can strengthen cybersecurity by implementing layered security architecture, enforcing strong authentication measures, conducting regular vulnerability assessments, establishing incident response plans, and promoting continuous cybersecurity awareness among students and staff.
4. Why is cybersecurity awareness important for students and faculty?
Human error is a major cause of cyber incidents. Training students, faculty, and administrative staff to recognize phishing attempts, manage passwords securely, and handle sensitive data responsibly significantly reduces the risk of security breaches.
5. How does strong cybersecurity support research protection in universities?
Effective cybersecurity safeguards intellectual property, research data, and confidential academic collaborations. By implementing access controls, secure networks, and monitoring systems, institutions can protect innovation and prevent unauthorized data access.
Latest
Trends blogs
- Closing the Digital Skills Gap: Challenges for Contemporary Education Policy
- Intelligent Learning Systems: The Rise of Agentic AI in Higher Education
- From Paper to Proof: How Blockchain is Reshaping Academic Credentials
- Executive Education in the AI Era: Shifting Models and New Realities